Your neighborhood ATM has always been a tempting target. From a physical attack standpoint, enterprising fraudsters drill holes to get at the USB slot, hide skimmers in the card readers, hammer them with bull dozers and explode them with bombs. They also play on the vulnerabilities of the cash dispenser, and one variation of that is Transaction Reversal Fraud (TRF). According to a recent report from the European Association for Secure Transactions (EAST), it was found that in 2019 there was an 87% increase in TRF (up from 4,843 to 9,054 incidents).
A form of a TRF attack, reported by NCR to have recently occurred in the United Kingdom, Ukraine and Canada, looks like this:
- A card and correct PIN are entered into the ATM
- A cash withdrawal is requested
- Cash is positioned behind the dispense shutter while the transaction in being authorized
- When the card is ejected from the ATM, the card is left in the slot until the transaction is timed out
- When the ATM tries to recapture the card, the fraudster introduces a fault at the ATM card reader, such as using a tool to hold the card in the reader
- A card jam is then reported and since no cash was dispensed, the ATM host application software logic reverses the card transaction
- The cash dispenser is then jammed open and the money positioned for dispensing is removed by the fraudsters – before the ATM has a chance to put the cash into the dispenser reject bin
In summary, a TRF is a sophisticated attack involving a sequence of events that generate multiple error codes and an unnecessary payment reversal. These attacks can be tricky to isolate and detect before financial losses occur, especially if changes to the ATM host applications are required. So what can you do to win?
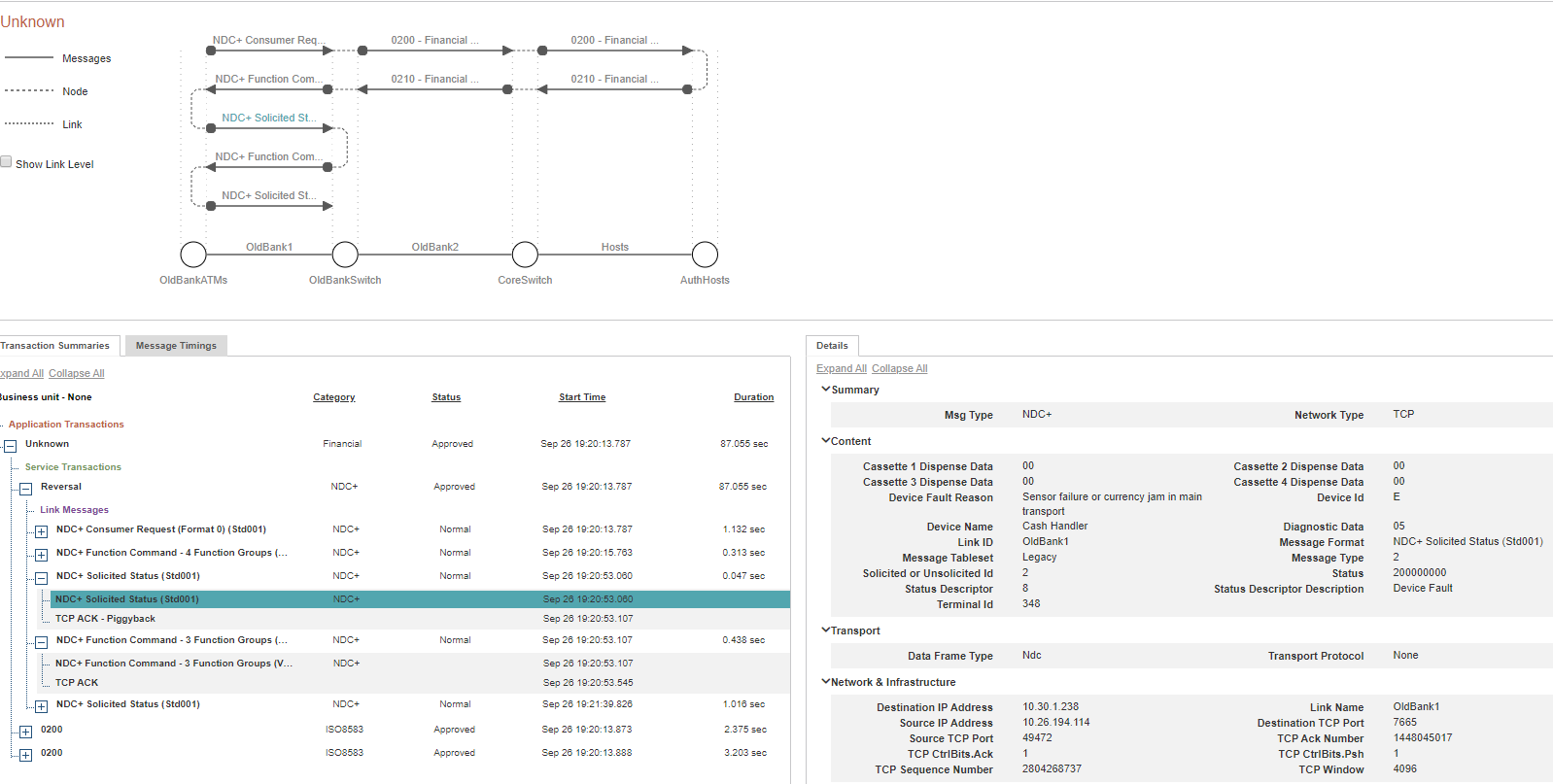
To detect and block TRF before major damage is done requires a powerful combination of real-time transaction data, multi-link transaction profiling and a customizable rules-based alerts engine to:
- Independently confirm that your ATM host applications are checking the currency dispenser status prior to approving the reversal of any transaction
- Quickly identify and research transactions associated with specific error codes
- Immediately flag reversal transactions, especially those that exceed specified withdrawal amounts or volume/velocity thresholds
Can you prevent Transaction Reversal Frauds?
It is impossible to prevent fraudsters from trying to pry open a cash dispenser, but with real-time access to the right data, you can gain the precise information needed to immediately detect TRF and protect (or even shut down) ATMs in seconds. When selecting a fraud detection and prevention solution, it is important that the solution have the ability to ensure that every payment transaction is independently captured, every message field is fully decoded and every transaction link is correlated, thereby providing you access to the underpinning data required to add real-time intelligence and visualization to your payment fraud strategy. Not only should the solution capture transaction data, it must marry transactions to hardware events and errors in real-time, thereby identifying transaction reversal frauds and helping take appropriate action.
If you would like to know more about INETCO Insight 7’s new fraud configuration, download our latest whitepaper, INETCO Insight – Machine Learning and Risk Scoring for Real-time Payment Fraud Detection and Prevention, here. Alternatively, if you would prefer to skip the read and just want to talk about where real-time fraud detection and prevention solutions are going, email me – I’d love to hear from you.